Most Intrusion Prevention Systems (IPS) export some type of machine log which contains all kinds of details related to the threats detected or that match certain criteria. Some IPS appliances are a bit more verbose and export details about every connection - kind of like NetFlow or IPFIX. For example the export from the Dragon IPS includes the details shown in the following figure:
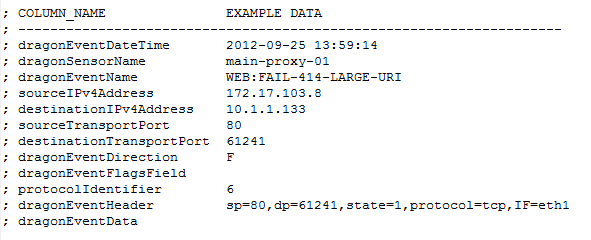
Notice in the above that several fields are similar to that exported by NetFlow capable switches.
- dragonEventDateTime
- sourceIPv4Address
- destinationIPv4Address
- sourceTransportPort
- destinationTransportPort
- protocolIdentifier
- dragonSensorName
- dragonEventName
- dragonEventDirection
- dragonEventFlagsField
- dragonEventHeader
- dragonEventData
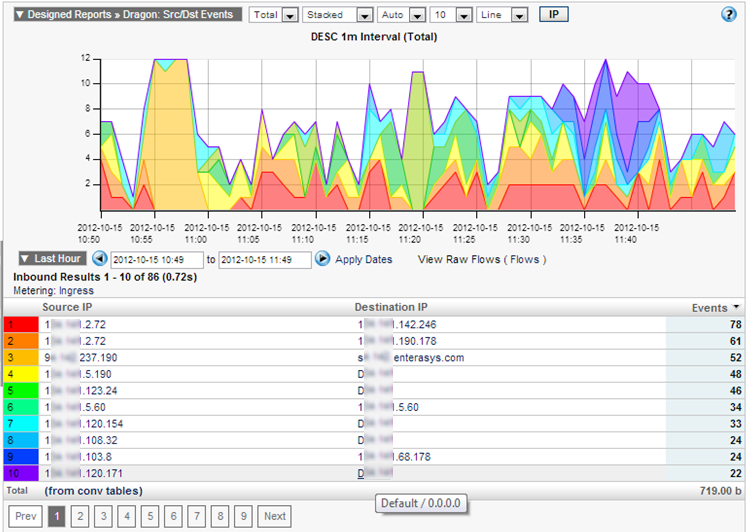
By leveraging IPFIXify, we can start exporting logs with IPFIX which supports a format similar to NetFlow. We can then trend the events that occurred over time. Compare this to a top applications report using NetFlow, sFlow or IPFIX:

By drilling in on one of the above Dragon “Event Names” or changing the report type, we can then view a report that looks very similar to another typical NetFlow trend. This is a great way to improve Dragon log reporting.
Collecting and warehousing all of the logs generated by network gear in a standard format ensure greater visibility and security across the enterprise because it means we point and search in one place.









Leave a comment