As you are probably aware, the Domain Name Server (DNS) plays an important role in how end users connect to the internet. In order to gain some background before reading this blog, you may want to read my post on An Overview of DNS. Once you have a bit more technical information on the DNS behaviors, I think you will find this post more informative.
DNS and Botnets
DNS is widely used by botnets to locate the Command and Control (C&C) servers. Because of improvements in detection technologies (e.g. man in the middle - SSL certificate proxying), botmasters can’t as easily rely on encrypted connections to hide their communications. Some have moved to hiding their messages on social network posts like twitter or news feeds. Another emerging technique used by bots to reach out to their C&C servers is domain-flux and fast flux. Source
Fast-Flux (IP-flux)
Fast-Flux involves rapid and repeated changes to A and/or NS resource records in a DNS zone, which have the effect of rapidly changing the location (IP address) to which the domain name of an Internet host (A) or name server (NS) resolves. Since blocking IP addresses will not work to defend against Fast-Flux activities, the security vendors have tried to cooperate in the process of suspending domains involved with Fast-Flux. Some registrars profiting from these activities have been resistant to blocking these Fast-Flux domains.
Another vantage of Fast Flux Service Networks (FFSN) is their high level of anonymity as the compromised hosts are usually set up as blind proxy redirectors which funnel ‘proxy’ the traffic to and from the backend servers which serve the actual, malicious content. By funneling the traffic, the blind proxy redirectors disrupt any attempt to track and reveal the identities of the backend servers. Consequently, this increases the life time of the backend servers and makes it simpler to set up and manage the backend servers. Even if we can locate these backend servers, it is difficult to take them down as they normally reside in complicit or hostile networks. Due to the high level of anonymity and resilience, FFSNs have been observed participating in many different types of malicious practices, such as illegal content hosting, malware distribution, online pharmacy shops, or phishing. FFSNs are normally part of the botnet and the nodes selected to be in the FFSN are selected from compromised hosts with a globally accessible IP address and high bandwidth. FFSNs hide the C&C channel and host the malicious code of the bot.
Blind Proxy Redirection
Redirection disrupts attempts to track down and mitigate fast-flux service network nodes. What happens is the large pool of rotating IP addresses are not the final destination of the request for the content (or other network service). Instead, compromised front end systems are merely deployed as redirectors that funnel requests and data to and from other backend servers, which actually serve the content. Essentially the domain names and URLs for advertised content no longer resolve to the IP address of a specific server, but instead fluctuate amongst many front end redirectors or proxies, which then in turn forward content to another group of backend servers. While this technique has been used for some time in the world of legitimate webserver operations, for the purpose of maintaining high availability and spreading load, in this case it is evidence of the technological evolution of criminal computer networks.
Domain-Flux
Where Fast-Flux changes the IP address used by the domain frequently, Domain-Flux changes the domain used by the malware frequently in an effort to hide their command and control servers. Often a domain generation algorithm (DGA) is employed. For example, The Conficker-A variant generated 250 domains every three hours using the current date and time as the seed value in order to make it difficult for vendors to pre-register domain names. The Conficker-C version randomly generated 50,000 domain names per bot. The seeds ensured all the bots generated the same domain names every day, according to researchers. Source
The problem with the Domain-Flux method is that every request sent by the bot to the DNS will trigger either the expected result (i.e. an IP address) or an NXDOMAIN message. An NXDOMAIN message is received by the DNS Resolver (i.e. bot) when a request to resolve a domain is sent to the DNS and the DNS cannot resolve it to an IP address (e.g. not found). An NXDOMAIN error message means that the domain does not exist. Imagine a client that is producing dozens of these every minute.
Monitoring NXDOMAIN messages is one of the responsibilities of our FlowPro Defender. Simply counting NX messages sent back to clients and triggering a threshold however, isn’t good enough and will often lead to lots of false positives. Although DNS traffic analysis alone can’t positively identify botnet activity, it can provide complementary evidence that when combined with the results of other threat detection methods.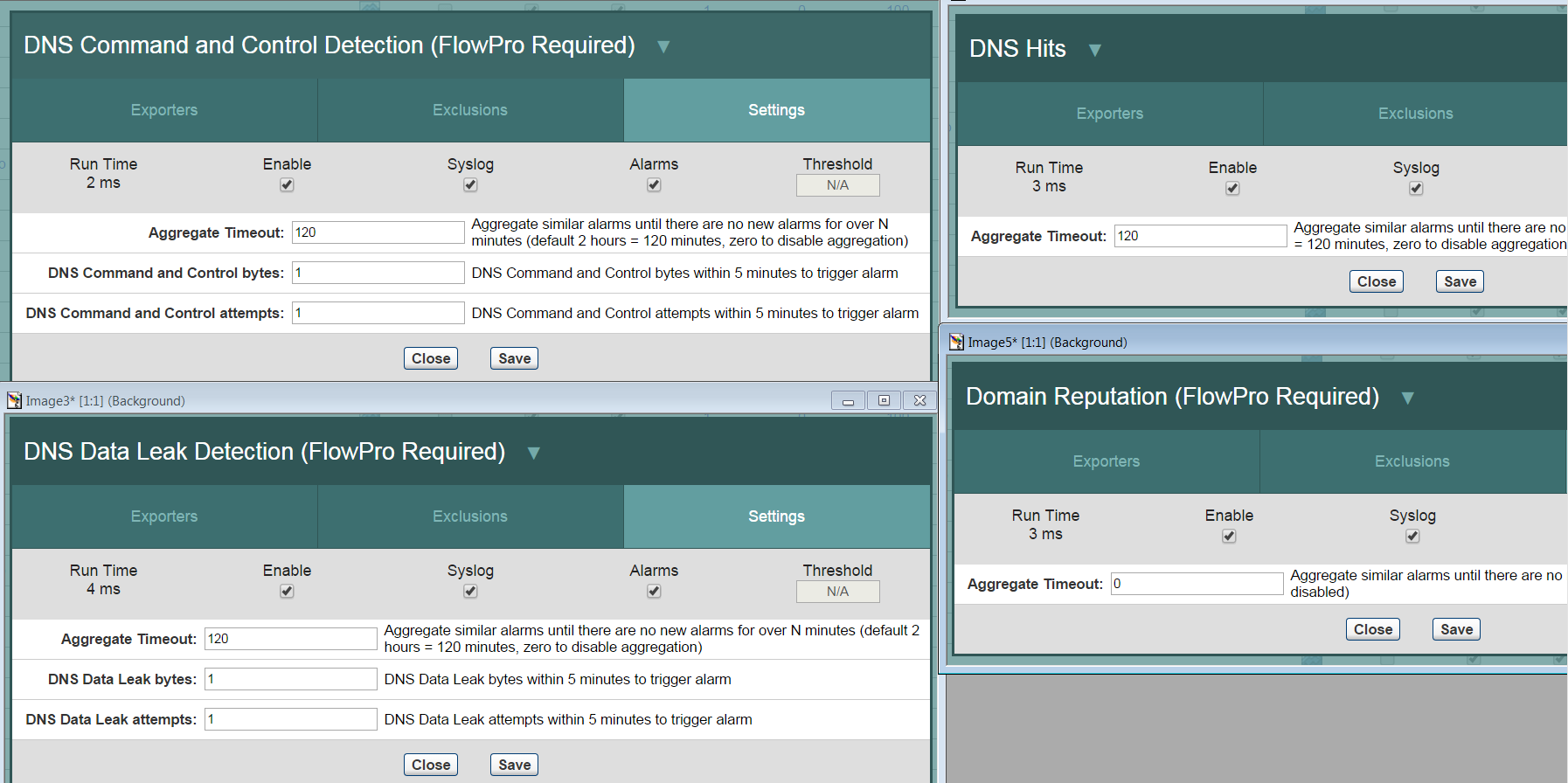
The correlation of these events increases the accuracy of botnet detection. More specifically, observing DNS traffic patterns can improve the detection of fast-flux and domain-flux related botnets.









Leave a comment