No matter how much reporting we have done on ransomware, the problem continues to get worse. And boy, have we written many stories about it. We told you in June about a $600,000 payment made to ransomware hackers and in the article, explained U.S. hacks have cost more than $3 trillion in ten years!
Another story we reported was 22% of small and medium businesses have been hit by ransomware.
Perhaps most interesting was the story about mayors vowing not to pay ransomware attackers anymore – as if that would stop the attacks. As expected – three days later we reported another attack taking place, La Porte County, Indiana got hit with Ryuk ransomware and their website and email went down.
Another incredible happening was as we wrote about the totality of ransomware attacks hitting cities this year, yet another city was hit – as we posted!
We continue to do our part – we posted an infographic titled How to Prevent Ransomware in the hopes that graphics will more easily allow people to understand the problem and how to solve it.
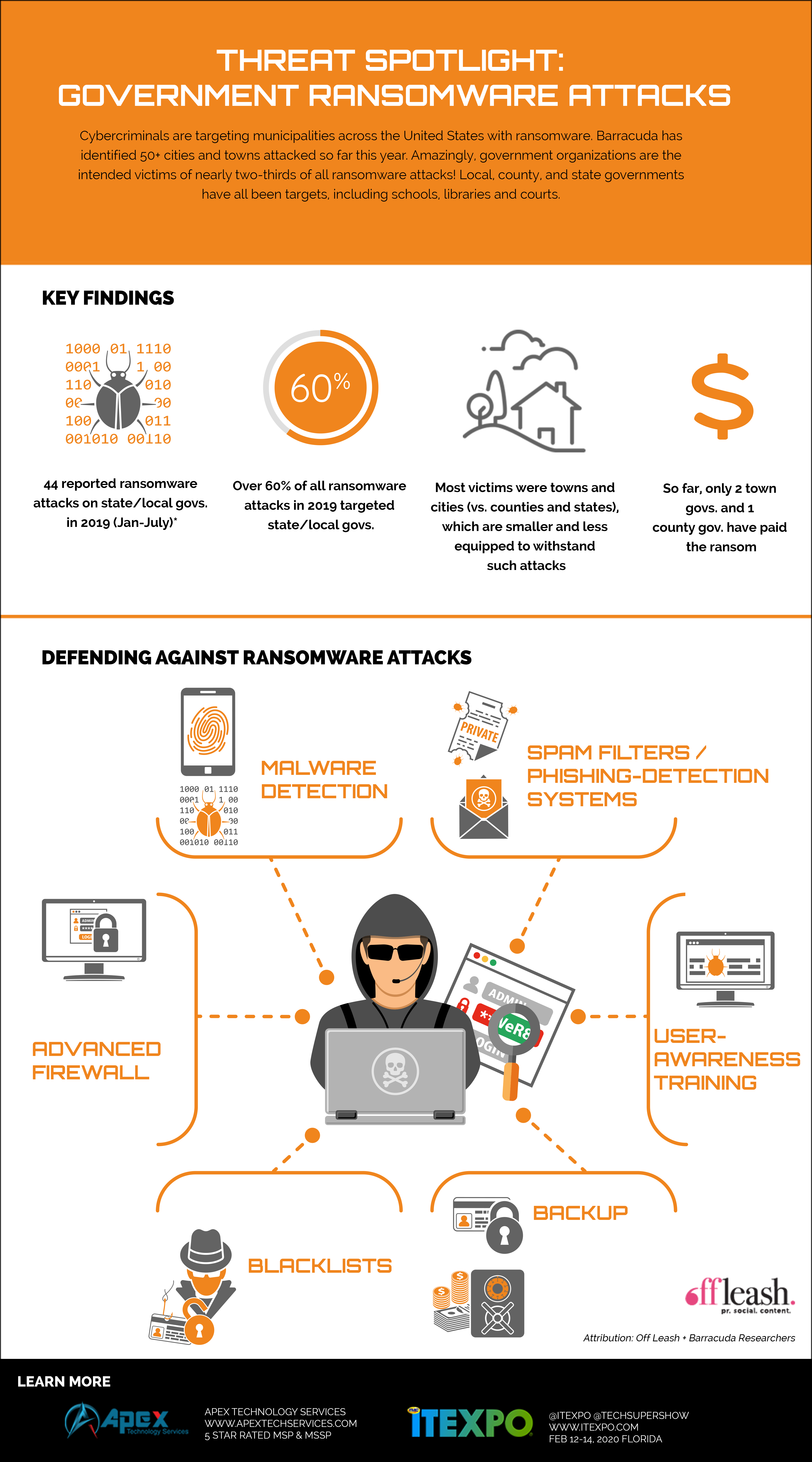
Today, Barracuda researchers have identified more than 50 cities and towns attacked so far this year. The team’s recent analysis of hundreds of attacks across a broad set of targets revealed that government organizations are the intended victims of nearly two-thirds of all ransomware attacks. Local, county and state governments have all been targets, including schools, libraries, courts, and other entities.
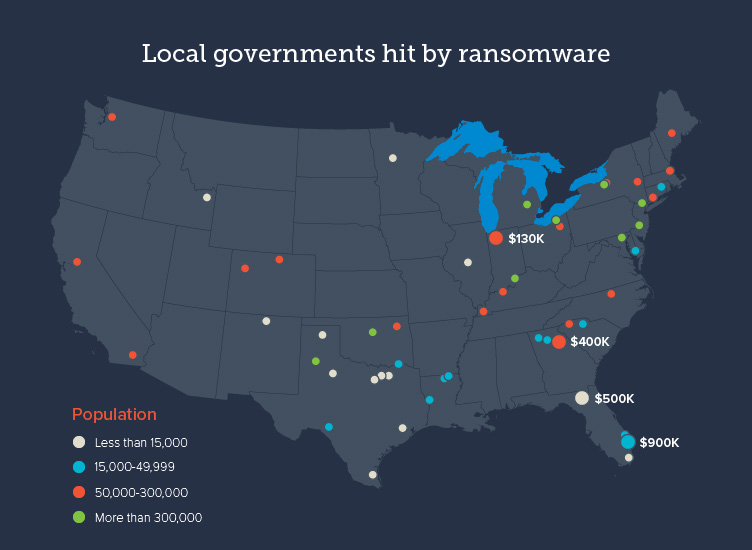
About 45 percent of the municipalities attacked had populations of less than 50,000 residents, and 24 percent had less than 15,000 residents. Smaller towns are often more vulnerable because they lack the technology or resources to protect against ransomware attacks. Nearly 16 percent of the municipalities attacked were cities with populations of more than 300,000 residents.
In the 55 attacks this year, only two town governments and one country government paid the ransom, all in June. In Florida, Lake City paid roughly $500,000 (42 Bitcoin), and Riviera Beach paid about $600,000 (65 Bitcoin), after trying and failing to recover their data. In Indiana, La Porte County paid $130,000 to recover its data. None of the cities attacked in 2019 so far have paid a ransom, including Baltimore, which spent $18 million to recover from the attack.
Ransomware used in recent attacks against state and local governments includes Ryuk, SamSam, LockerGoga and RobbinHood.
Barracuda researchers see attacks like this against government organizations on a regular basis. Email is the most common threat vector for these types of ransomware attacks but the blast radius can easily reach networks, applications and a wide variety of sensitive and critical data.
While this study focused on attacks in the United States, there have been similar attacks globally, with attacks hitting four communities of varying sizing in Canada as well the Dublin tram system in Ireland and power utilities in India and South Africa.
The exclusive infographic above sums it up and has ideas on how to prevent ransomware in your organization.
In addition, we suggest:
1) Read cybersecurity essentials – a simple list which will help most organizations become far more secure.
2) Go to a phishing simulation vendor now and sign up for one of their offerings. Phishing Box, KnowBe4 and Phish360; are all great.
3) We also recommend you get a free evaluation of your cybersecurity risk from an MSP/MSSP immediately – they can also help you build in the needed compliance to reduce the risk of being fined.
4) Finally, Learn about the latest in everything you need! Cybersecurity, the Channel, IT, IOT, Edge, AI, SD-WAN, and the Future of Work at the world’s only MSP Expo, part of the ITEXPO #TechSuperShow, Feb 12-14, 2020 Fort Lauderdale, FL.