Computers, phones, IoT devices, everything can be hacked. As a result, SD-WAN vendors are teaming with firewall companies to develop SASE solutions that allow secure application delivery from the cloud to the device. Sadly, the telecom network is still vulnerable. We have known for years the SS7 network – which provides the underlying telecom signaling in the networks of companies like AT&T and Verizon is full of security holes.
The only thing protecting us is the difficulty for a typical hacker to learn enough to hack such a network. This isn’t the case for nation-states of course.
Positive Technologies just released a report which outlines security flaws it discovered in LTE and 5G networks that could enable criminals to leave an entire city without communications, impersonate users, and get free mobile service at the expense of an operator or customer.
The report finds that most of today’s 5G networks, just like 4G ones, are vulnerable to the following types of attacks:
- Disclosure of subscriber information (including TEID and location data)
- Spoofing, which can be used for fraud and impersonation attacks
- DoS attacks on network equipment, resulting in mass disruption of mobile communication

Dmitry Kurbatov, CTO at Positive Technologies commented, “Every network tested was found to be vulnerable to DoS, impersonation and fraud. In practice, this means that attackers could interfere with network equipment and leave an entire city without communications, defraud operators and customers, impersonate users to access various resources, and make operators pay for non-existent roaming services. Moreover, the risk level is very high: some of these attacks can be performed using just a mobile phone.”
Kurbatov continued: “The non-standalone arrangement, planned as temporary, will be the only available option for the next few years as 5G core standalone is being established. Therefore, we can say that most of today’s 5G networks, just like 4G ones, are vulnerable to these types of attacks. This makes the security vulnerabilities of the GTP protocol urgent – as the increased use of 5G vastly increases the damage an attack such as a denial of service attack could do.
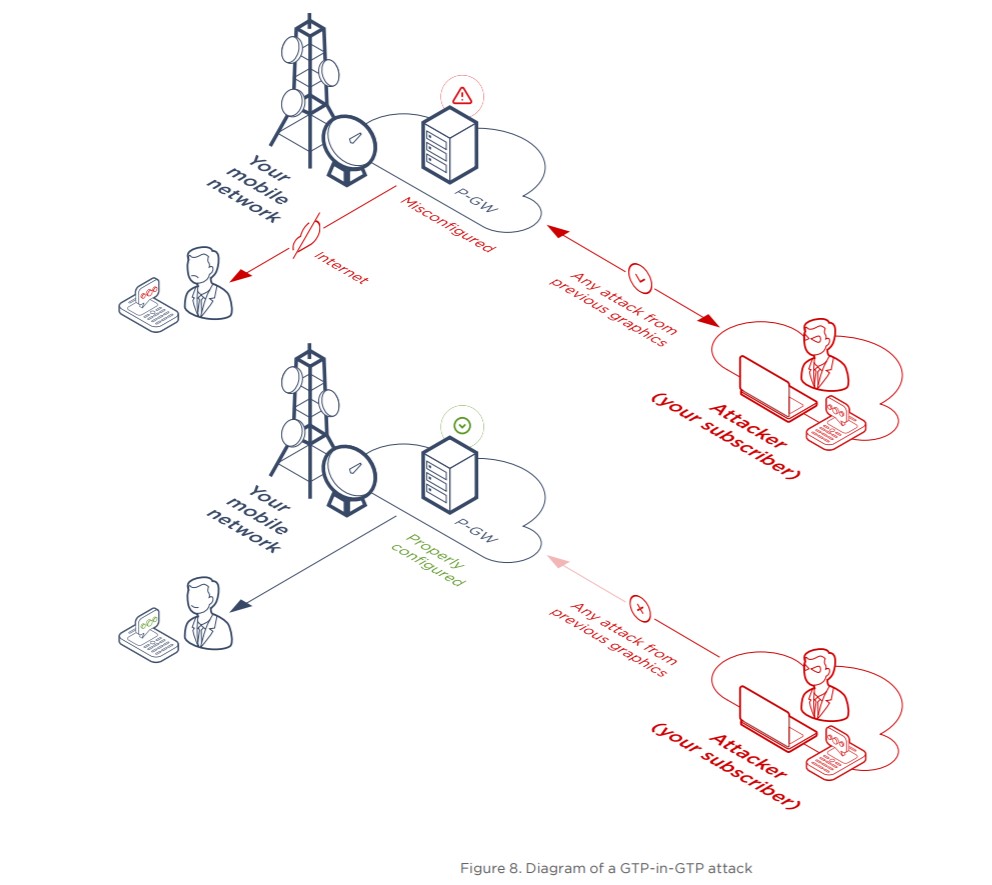
“Currently, operators are putting very few security measures in place to protect against these vulnerabilities and are also making configuration mistakes that are putting their networks at further risk. We urge operators to read this research and pay more attention to the GTP protocol and follow the recommendations of the GSMA FS.20 GPRS Tunnelling Protocol (GTP) Security, including implementing ongoing monitoring and analysis of signalling traffic to detect potential security threats. With the roll-out of 5G these issues have never been more important – attempts to implement security as an afterthought at later stages may cost much more so security has to be a priority during network design.”
For more, see Carl Ford’s post from a few years back discussing SS8 or the lack thereof.
See the ONLY 5G, SD-WAN, Contact Center, Tech and Communications companies that matter at the ITEXPO #TECHSUPERSHOW.
This Event has been called the BEST SHOW in 5 YEARS and the Best TECHNOLOGY EVENT of 2020.
2020 participants included: Amazon, Cisco, Google, IBM, ClearlyIP, Avaya, Vonage, 8×8, Comcast Business, BlueJeans, CoreDial, Dell, Edify, Epygi, FreeSWITCH, Fuze, Grandstream, Granite, Intrado, Frontier Business, Fujitsu, Jenne, West, Konftel, Intelisys, Martello, NetSapiens, OOMA, Oracle, OpenVox, Peerless Network, Phone Sentry, Phone.com, Poly, QuestBlue, RingByName, Sangoma, SingTel, SkySwitch, Spracht, Spectrum, Sprint, Tallac, Tech Data, Telarus, TCG, Teledynamics, Teli, Telinta, Telispire, Telstra, TransNexus, Unified Office, Vital PBX, VoIP Supply, Voxbone, VoIP.MS, Windstream, XCALY, XORCOM, Yealink, Yubox, and ZYCOO. Full List.
Join 8K others with $25B+ in IT buying power who plan 2021 budgets! Including 3,500+ resellers!
A unique experience with a collocated Future of Work Expo, SD-WAN Expo, and MSP Expo…