Companies have a challenge that as more data has moved to cloud apps, they have lost the traditional visibility, threat detection and control they used to enjoy. As they evolve from a CAPEX model to OPEX in search of best-in-breed apps, there remains a large security hole which needs filling.
This is where elastica (recently out of stealth mode) comes in… In a conversation with Eric Andrews VP of Marketing and Rehan Jalil President & CEO, they told me that companies need to be able to track activity in and out of these cloud services. They attack security through a suite of cloud-based services as follows:
- Their AUDIT shadow IT solution looks at the SaaS apps being used and reports how vulnerable each one is. It updates regularly – as frequently as 15 minutes.
- DETECT threats solutions detects intrusions in cloud app usage – for example, when a user is acting maliciously or behavior is suspicious, an organization is alerted.
- PROTECT cloud data stops policy violations from happening across cloud apps.
- INVESTIGATE transactions is like a network DVR function for your cloud applications.
The solutions can see firewall and other data and is aware of the users in the organization – they are placed in various groups. You can select from the above-four solutions in their cloud app-store and also opt for “securelets” which are mini-apps which correspond to the cloud services you are looking to monitor and secure.
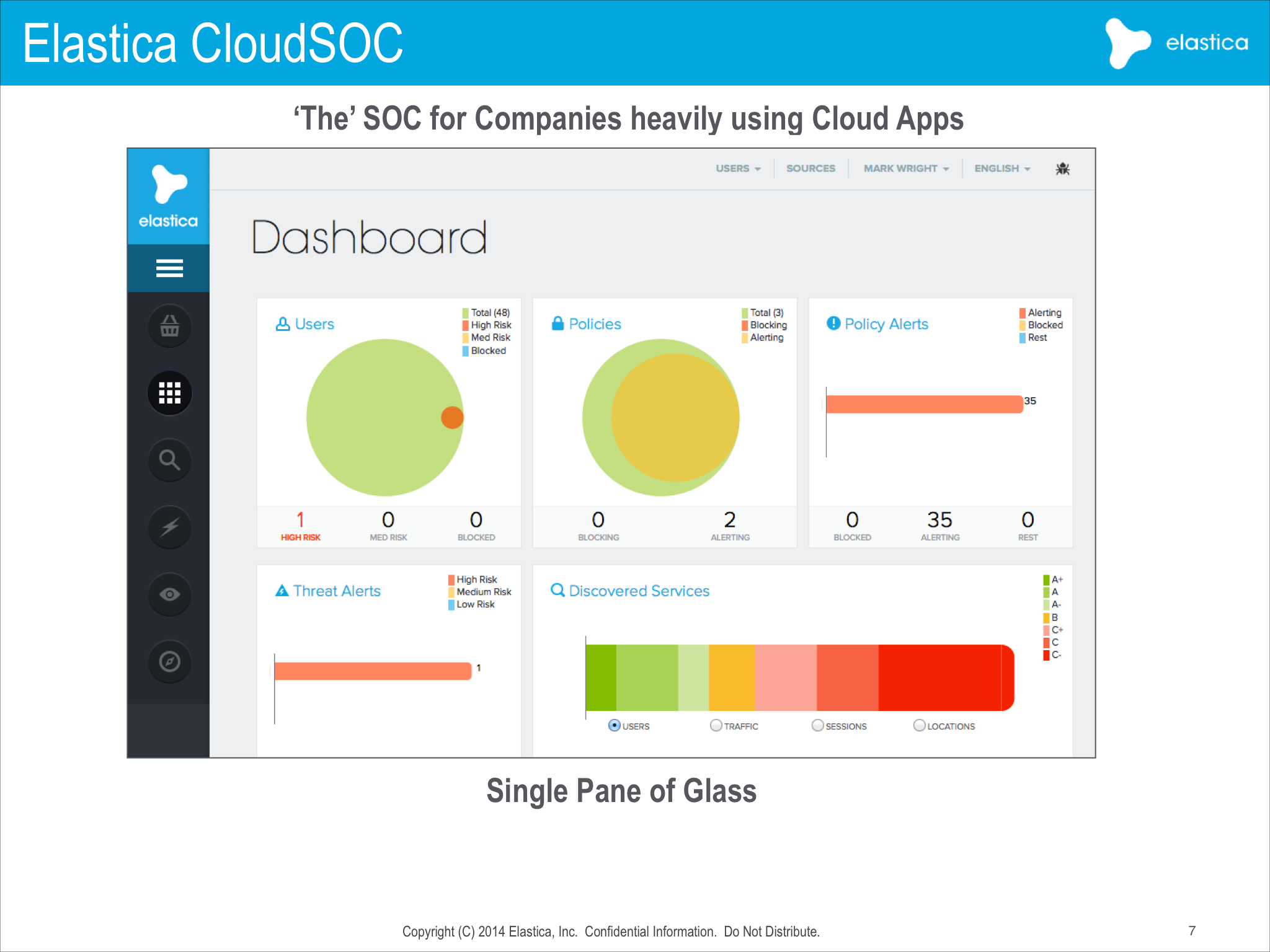
Using the system’s dashboard, you can determine user location and activity within applications. When a user tries to do something like send a file they aren’t allowed to send, the system blocks this activity and further alerts the administrator through a dashboard and other alert.
You can then drill down into a user’s activities to see what apps they use and what they do in said applications.
You can further determine on a group basis what users can do in each cloud app – or across a range of apps. In other words you may specify certain users can’t send certain files regardless of application. Moreover, using a threat score, you can stop certain activities from happening. Moreover, if a user starts to download massive amounts of data which is unusual for them or they use a different IP address and engage in unusual behavior, their threat level automatically is increased thanks to the system’s machine-learning capability.
Administrators can be alerted of security events or threat level increases. A single dashboard enables a company to determine which users are malicious, where are attacks are coming from and which apps are the most threatening.
The idea is they are rebuilding the SOC in the cloud for the cloud so a SISO could determine what is happening in the organization.
The elastica dashboard in action