Industrial cybersecurity is a major problem as older systems are often not updated to handle current threats. Moreover, they are connected to IT systems which have internet access. Hackers use spear-phishing to get access to user credentials. From there, they search the network for industrial control system. They then recreate the control system to ensure they know how it works. At this point they can remotely control the system.
This is a basic take off on the Stuxnet virus the U.S. and Israel were said to have used against Iran centrifuges.
Targeting critical infrastructure has been done by Russia – we reported LockerGoga targeting Norsk Hydro – a hack which cost $40M in the first week alone! We further reported Russia penetrated electric utility control rooms in the U.S.
“They got to the point where they could have thrown switches” to disrupt the flow power, Jonathan Homer, chief of industrial-control-system analysis for DHS, told the Wall Street Journal.
Then there was NotPetya, the $10B Russian malware which was highly malicious and targeted. It used ransomware tactics but did not allow the targeted organizations to get their data back.
Iran attacked a dam in Rye in 1995, New York, in Westchester County as well as many financial institutions in New York City.
This is the opportunity… Stopping the havoc being wreaked by nation-states. And we expect the situation to get far worse. Details are now emerging about how the NSA and U.S. Cyber Command created a secret task force ARES and Operation Glowing Symphony to take out the cyber capabilities of ISIS. The U.S. government has decided to make the world aware of its cyber capabilities – hoping this will act as a deterrent.
They go into a great deal of detail on what they can do. It may or may not stop enemies from attacking American targets. Another potential outcome is an emboldened enemy looking to emulate and one-up the capabilities of U.S. government hackers.
Sadly, U.S. business and industrial systems are on the front lines of this cyber war.
In June of this year we told you about Honeywell Forge bringing analytics and action to IoT. More recently, our colleague Ken Briodagh at IoT Evolution wrote Honeywell Building Integration and Cyber Solutions Suite to Improve Efficiency, Data Analysis and Control.
In both cases, we touched on the company’s cybersecurity efforts.
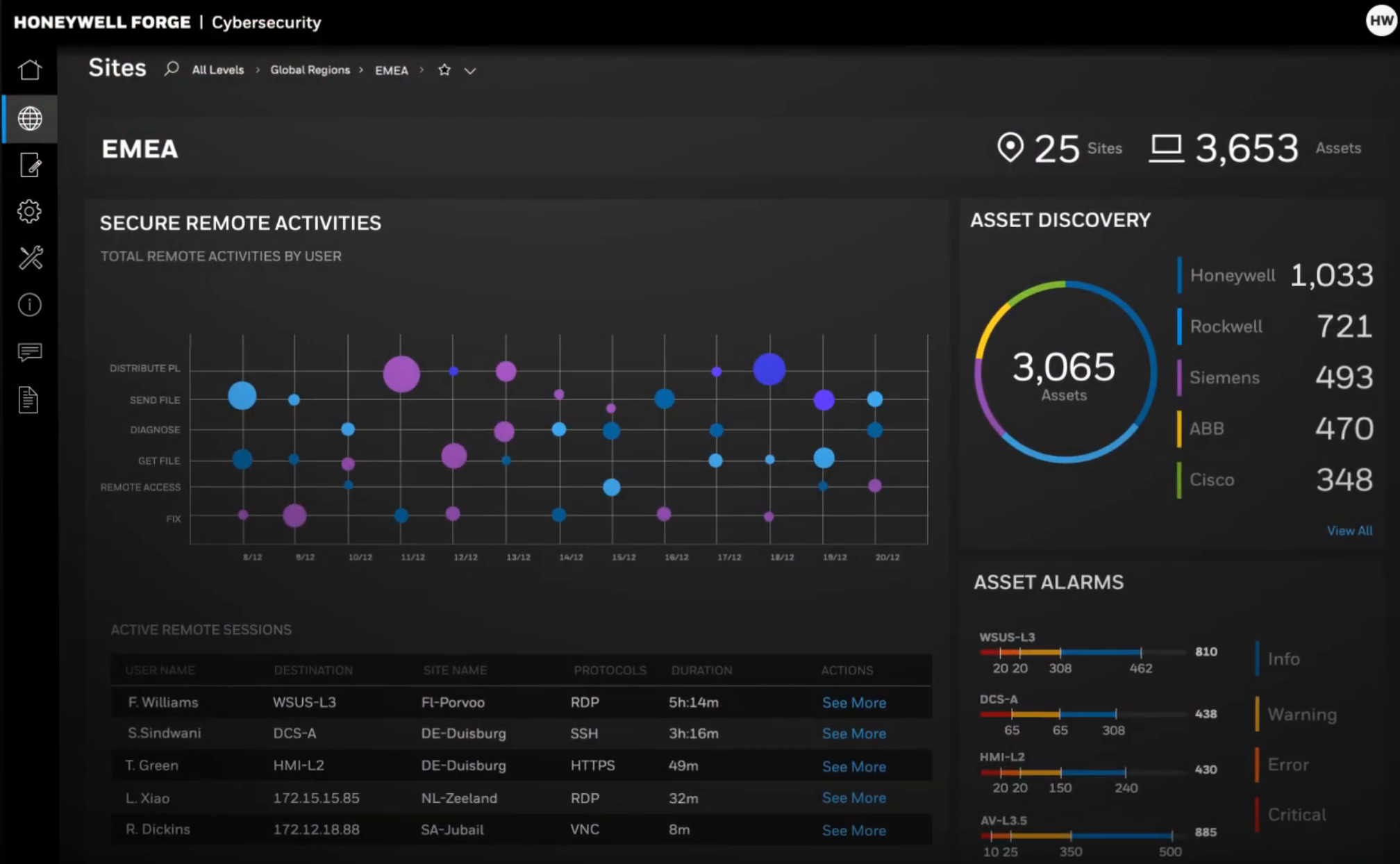
They have now formalized their solution – the Honeywell Forge Cybersecurity Platform improves cybersecurity performance at a single site or across an enterprise by increasing visibility of vulnerabilities and threats, mitigating risks, and improving cybersecurity management efficiency. The Honeywell Forge Cybersecurity Platform is part of the Honeywell Forge for Cybersecurity portfolio of products and services that increases cybersecurity across industrial environments.
The new platform safely moves data from one site to another and uses operations data to strengthen endpoint and network security, and improves cybersecurity compliance. The platform also delivers a scalable software solution to better address cybersecurity pain points in OT and IIoT environments.
“Honeywell Forge for Cybersecurity is a big step forward in the company’s overall cybersecurity strategy. The unified suite of applications, services and products can address a range of end-user cybersecurity requirements from asset discovery and monitoring and Secure Remote Access to fully managed services,” said Larry O’Brien, vice president of research at ARC Advisory Group. “Honeywell Forge Cybersecurity Platform represents a common approach to OT-level cybersecurity that recognizes the impact of IoT on manufacturing, including the monitoring of virtual machines, firewalls, and other assets in industrial environments.”
Based on technology installed in thousands of sites globally, the Honeywell Forge Cybersecurity Platform improves cybersecurity performance by giving customers the tools they need to strengthen their cybersecurity operations and asset management, all through a single dashboard. In addition, multi-site, multi-vendor capabilities support an enterprise-wide solution with greater efficiencies and lower total cost of ownership regardless of the control system used.

“Customers now have a better choice to strengthen industrial cybersecurity across their enterprise to enable IT-OT convergence and digital transformation, improving enterprise performance while reducing the cost of cybersecurity,” said Jeff Zindel, vice president and general manager, Honeywell Connected Enterprise, Cybersecurity. “The Honeywell Forge Cybersecurity Platform provides multiple industry-proven capabilities in a single dashboard to simplify cybersecurity management and better protect people, processes and assets from evolving cyberthreats.”
The Honeywell Forge Cybersecurity Platform is available in three versions, allowing customers to scale when needed to match cyber-requirements and budget with Enterprise Core, Enterprise Premium and Site offerings.
Customers that may not have the cybersecurity expertise or resources to support the Honeywell Forge Cybersecurity Platform, but want to get the most out of their cybersecurity investment, can benefit from Honeywell’s Managed Security Services to host and run the software. With experts in industrial cybersecurity around the world, Honeywell provides Cybersecurity Consulting Services to complement the Honeywell Forge Cybersecurity Platform to help further strengthen cyber defenses.
The Honeywell Forge Cybersecurity Platform is part of Honeywell Forge, a new category of software solutions that deliver Enterprise Performance Management for Operations Technology to aerospace, building, industrial and worker segments. Honeywell Forge was launched earlier this year to improve the way a variety of companies collect, analyze and act on data from their operations.
In addition, we suggest all organizations do the following to stay secure:
- Read cybersecurity essentials – a simple list which will help most organizations become far more secure.
- Go to a phishing simulation vendor and sign up for one of their offerings. Phishing Box, KnowBe4 and Phish360; are all great. This is needed to train workers by testing them without their knowledge by sending real-looking emails to their inboxes. If they click, they are immediately trained on what not to do.
- We also recommend you get a free evaluation of your cybersecurity risk from an MSP/MSSP immediately – they can also help you build in the needed compliance to reduce the risk of being fined
Finally – register for the ITEXPO #TechSuperShow, Feb 12-14, 2020 Fort Lauderdale, FL. to learn about the latest in IoT, IIoT and Cybersecurity.